Independent backup validation. Signed evidence for your auditor or agent.
Riskora performs independent restore validation on your SQL Server and Azure environment, detects integrity failures before they become recovery failures, and delivers signed, immutable evidence your auditor or insurer will accept.
Scope Your Environment See how it worksAuditors and insurers want proof. Most IT teams can't produce it.
Ransomware targets backup chains first. Manual restore drills are expensive, rarely happen on schedule, and almost never produce documentation that holds up under audit. When the questionnaire arrives, most IT Directors are working from memory, not evidence.
Audit & compliance pressure
SOC 2, ISO 27001, and HIPAA controls require documented backup testing. Spreadsheets and screenshots don't hold up.
Cyber insurance renewal
Insurers are requiring backup integrity attestation. Organizations without documented evidence face higher premiums or declined coverage.
Poisoning hides in plain sight
Subtle data drift and integrity failures can go undetected for weeks — until recovery is needed and the backup is useless.
How Riskora Works
Four scoped steps, every engagement.
Environment scoping
We map your SQL Server and Azure backup infrastructure — native backups, third-party tools like Veeam or Commvault, retention schedules — and confirm requirements directly with your auditor or insurance agent before any work begins. The evidence package is built to their spec from day one, not revised after the fact.
Isolated restore validation
Selected snapshots restored into isolated, locked-down environments. No production access. No credentials stored beyond the engagement. Results are logged with full chain of custody.
Integrity & poisoning analysis
Checksum and manifest verification against your SQL Server backup metadata. Schema consistency checks, row-count validation, and drift detection. We look for what a successful backup job status doesn't tell you.
Signed evidence delivery
Signed PDF and JSON artifacts mapped to your specific framework controls. Ready to hand to an auditor or attach to an insurance submission. No interpretation required on their end.
What you receive
Every engagement delivers a complete, auditor-ready evidence package. Not a dashboard. Signed, immutable documentation.
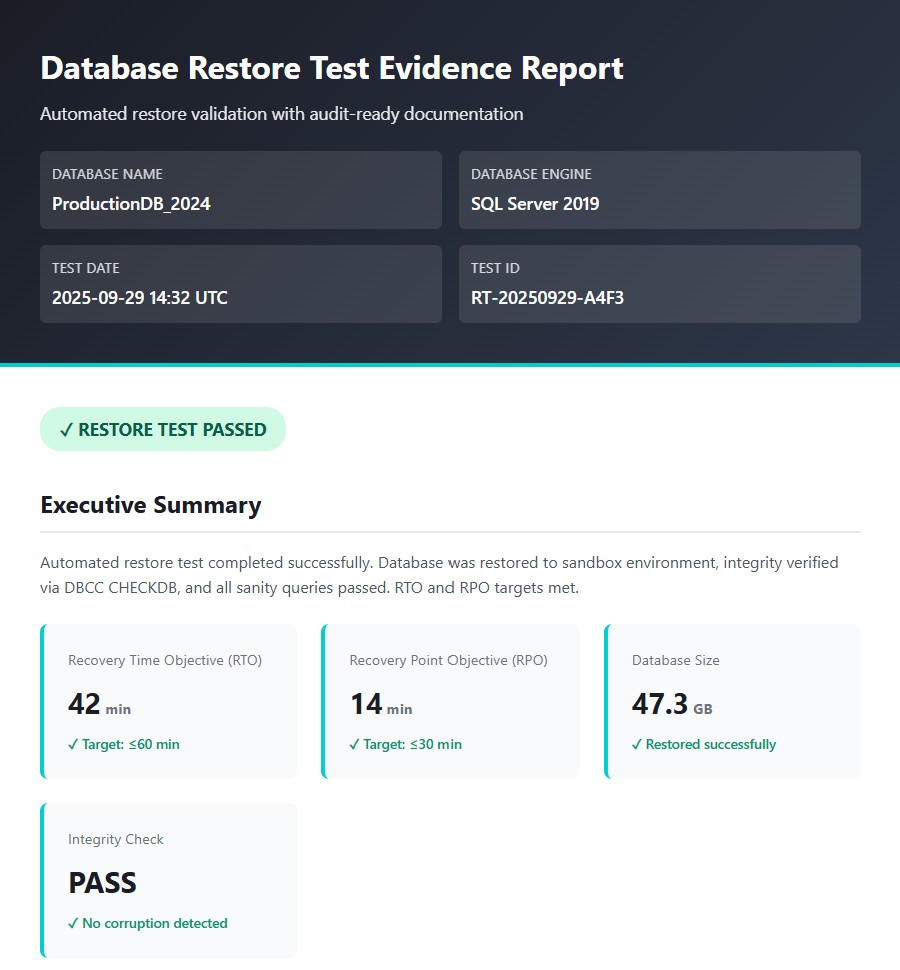
Restore validation report
Dated, signed record of each restore test: database, snapshot, duration, outcome, and findings. Written for an auditor, not an IT team. Chain of custody intact from backup to restored state.
Integrity & poisoning findings
Findings from checksum verification, schema consistency analysis, and row-count validation against your SQL Server backup metadata. Clean results documented. Issues flagged with specificity, not ambiguity.
Framework-mapped evidence pack
Artifacts cross-referenced to your specific control requirements — SOC 2, ISO 27001, HIPAA, or cyber insurance questionnaire line items. Built to the spec your auditor or agent confirmed before the engagement started.
Immutable ledger record
SHA-256 hash chain with WORM/Object Lock storage and optional blockchain anchoring. Tamper-evident by design.
SQL Server and Azure coverage
On-premises SQL Server, Azure SQL Database, and Azure SQL Managed Instance. Native backup support plus third-party tools including Veeam and Commvault running in your SQL environment.
Recommended validation cadence
Based on your audit cycle and insurer requirements, we provide a recommended validation schedule so your evidence stays current and you're never scrambling before a renewal deadline.
Frequently Asked Questions
Do you need production credentials?
No. We operate with least-privilege and read-only access. Restores occur in isolated sandboxes with strict network policies. No credentials are stored beyond the engagement.
What backup platforms are supported?
We work with SQL Server on-premises, Azure SQL Database, and Azure SQL Managed Instance. For backup tooling, we support native SQL Server backups as well as third-party solutions including Veeam and Commvault running in your SQL environment. Contact us to confirm coverage for your specific setup.
How is audit evidence stored?
All validations are hashed and signed. Artifacts are stored in WORM/Object Lock stores with optional blockchain anchoring — tamper-evident and ready for external review.
How does the engagement begin?
With a scoping conversation. We confirm your infrastructure, your compliance framework requirements, and your audit or renewal timeline before any work begins. Most engagements scope in a single call.
Can you work directly with our auditor or insurance agent?
Yes. We'll engage with them directly to confirm exactly what format, control mapping, and level of detail they require before we produce anything. Our role is to deliver independent evidence — not to interpret or advocate — so direct coordination with your auditor is a natural fit. It eliminates the back-and-forth that happens when evidence packages get revised after submission.
Every engagement begins with a scoping conversation.
Tell us what you're facing — audit deadline, insurance renewal, or an inherited SQL Server environment you've never actually tested — and we'll confirm fit, engage your auditor or agent directly, and outline what the engagement looks like.
We respond within one business day.